- install
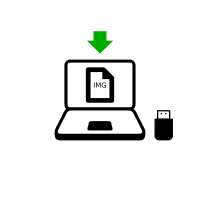
- Baixe e verifique (para pendrives USB)
Baixe o Tails

or download using BitTorrent BitTorrent
Save your download to your usual Downloads folder and not to the USB stick.
We recommend that you save your download to your Persistent Storage. Otherwise, Tails might stop responding if the RAM memory of the computer gets full.
Enquanto o arquivo baixa, recomendamos que você leia as notas de lançamento do Tails 6.2 . Elas detalham todas as mudanças nesta nova versão: novas funcionalidades, problemas que foram solucionados, e problemas conhecidos que já foram identificados.
Verifique seu download



Verifique o arquivo baixado para ter certeza de que é seguro e não foi corrompido durante o download.
Seu cliente BitTorrent verificará automaticamente seu download quando ele terminar.
A verificação abaixo é opcional para um download feito via BitTorrent.
Você parece ter JavaScript desativado. Para verificar seu download, você pode:
Habilitar JavaScript e recarregar esta página.
Compare manually the checksum of your download with the checksum of our images. In Tails, you can install GtkHash as Additional Software
Verify your download using our OpenPGP signing key and OpenPGP signature. OpenPGP signature.
Nós não fornecemos mais instruções para verificação de downloads usando OpenPGP.
Veja nossa análise de segurança das diferentes técnicas de verificação.
Você parece estar usando Internet Explorer. Para verificar seu download, use um navegador diferente.
ou verifique usando a assinatura OpenPGP
OpenPGP signature OpenPGP signature
Se você não sabe como usar a assinatura OpenPGP, clique no botão Selecione seu download… para verificar seu download usando JavaScript.
Verificando $FILENAME…
![]() Verificação bem
sucedida! ($FILENAME)
Verificação bem
sucedida! ($FILENAME)
![]() Falha na
verificação! ($FILENAME)
Falha na
verificação! ($FILENAME)
O mais provável é que a verificação tenha falhado por causa de um erro ou de uma interrupção durante o download.
A verificação também falha quando se tenta verificar um download de uma versão do Tails que não seja a mais recente: 6.2 .
Com menor probabilidade, a verificação pode ter falhado por causa de um arquivo malicioso baixado de um de nossos espelhos, ou por causa de um ataque na rede do seu país ou na sua rede local.
Fazer uma nova tentativa de baixar geralmente é o suficiente para consertar esse problema. Caso não funcione, por favor tente baixar em um lugar diferente ou em um computador diferente.
![]() Erro ao selecionar a
imagem.
Erro ao selecionar a
imagem.
Verifique se a imagem USB que você escolheu pode ser lida pelo seu navegador.
Tenha certeza de ter escolhido uma imagem ISO que possa ser lida pelo seu navegador.
![]() Erro ao tentar baixar
um arquivo de checksums do nosso
site.
Erro ao tentar baixar
um arquivo de checksums do nosso
site.
Verifique se seu navegador está conectado à Internet.
![]() Erro ao ler imagem
$FILENAME.
Erro ao ler imagem
$FILENAME.
Tenha certeza de que $FILENAME pode ser lido pelo seu navegador.
Continue instalando ou atualizando o Tails
Com esta imagem USB, você pode fazer um dos seguintes:
Upgrade your Tails USB stick and keep your Persistent Storage.
Install a new Tails USB stick.
To burn a Tails DVD, download our ISO image instead.
Warnings: Tails is safe but not magic!
Tails é mais seguro do que qualquer sistema operacional comum. Apesar disso, nem o Tails nem qualquer outro programa ou sistema operacional pode te proteger de tudo - mesmo que finjam poder.
As recomendações abaixo te trarão ainda mais segurança, especialmente se você estiver sob grande risco.
Protegendo sua identidade durante o uso do Tails

Tails é feito para esconder sua identidade.
Mas algumas das suas atividades podem acabar revelando a sua identidade:
- Compartilhar arquivos com metadados, como data, hora, local e informações sobre o dispositivo
- Usar Tails para mais de um objetivo por vez
Limitações da rede Tor

Tails usa a rede Tor porque é a mais forte e popular rede para se proteger de vigilância e censura.
Mas a rede Tor é limitada caso você precise:
- Esconder o fato de que você está usando Tor e Tails
- Proteger suas comunicações online de atacantes determinados e habilidosos
Reduzindo riscos ao usar computadores não confiáveis
Tails pode ser executado com segurança em um computador que esteja com vírus.
Mas Tails pode acabar não te protegendo se:
- For instalado a partir de um computador infectado
- For executado em um computador com BIOS, firmware ou hardware comprometidos
Protegendo sua identidade durante o uso do Tails
Limpe os metadados de arquivos antes de compartilhá-los
Vários arquivos contêm dados escondidos, ou metadados:
JPEG e outros formatos de arquivos de imagens geralmente contêm informações sobre onde a foto foi tirada e qual câmera foi utilizada.
Documentos de Office geralmente contêm informações sobre o autor, além da data e hora em que o documento foi criado.
Para te ajudar a limpar metadados, Tails inclui o Matadata Cleaner, uma ferramenta que remove metadados de uma grande quantidade de formatos de arquivos.
Metadados já foram usados no passado para localizar pessoas através fotos que elas tiraram. Veja, por exemplo NPR: traído pelos metadados, John McAfee admite que realmente está na Guatemala (em inglês).
Use sessões do Tails para apenas um propósito por vez
Se você usar uma sessão Tails para mais de um propósito por vez, um adversário poderá conseguir associar suas diferentes atividades uma à outra.
Por exemplo, se você logar em contas diferentes em um mesmo site usando a mesma sessão do Tails, este site poderá identificar que as contas diferentes estão sendo utilizadas pela mesma pessoa. Isso ocorre porque os sites conseguem saber quando duas contas diferentes estão usando o mesmo circuito Tor.
Para evitar que um adversário consiga associar suas diferentes atividades uma com a outra durante o uso do Tails, reinicie o Tails entre as diferentes atividades. Por exemplo, reinicie o Tails depois de checar sua conta de email do trabalho e antes de checar sua conta de email utilizada para denúncias.
Nós não temos conhecimento de nenhum ataque que possa desanonimizar pessoas online que tenham usado Tails para um propósito diferente por vez.
Se você se preocupa com a possibilidade de que os arquivos no seu Armazenamento Persistente sejam utilizados para associar suas diferentes atividades, pense na possibilidade de usar um pendrive USB com Tails para cada atividade diferente. Por exemplo, use um pendrive USB com Tails para seu trabalho de ativismo e outro para o seu trabalho de jornalismo.
Limitações da rede Tor
O uso do Tails deixa explícito os fatos de que você está usando a rede Tor e, provavelmente, Tails
Tudo que você faz na internet a partir do Tails passa pela rede Tor.
Quando Tor e Tails te protegem, não é fazendo você parecer um usuário aleatório de Internet, mas sim fazendo com que todos os usuários de Tor e Tails pareçam ser o mesmo. Assim torna-se impossível distinguir quem é quem entre esses usuários.
O seu provedor de serviço de internet e a sua rede local podem ver que você conecta à rede Tor. Ainda assim, não sabem quais sites você visita. Para esconder o fato de que você está usando Tor, use uma ponte Tor.
Os sites que você visita podem saber que você está usando Tor, pois a lista de nós de saída da rede Tor é pública.
Controles parentais, provedores de serviço de Internet e países com censura pesada podem identificar e bloquear conexões com a rede Tor que não estejam usando pontes Tor.
Vários sites pedem que você preencha um CAPTCHA ou mesmo bloqueiam o acesso a partir da rede Tor.
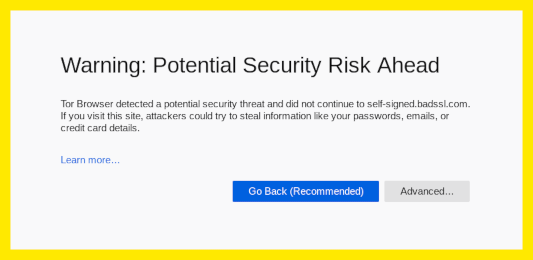
Nós de saída podem interceptar tráfego para o servidor de destino
A rede Tor oculta a sua localização para os servidores de destino, porém não criptografa toda sua comunicação. O ultimo retransmissor do circuito Tor, chamado nó de saída, estabelece a conexão final com o servidor de destino. Esta ultima etapa pode não ser criptografada, por exemplo no caso de conexões a websites usando HTTP ao invés de HTTPS.
O nó de saída pode:
Observar seu tráfego. É por isso que o Navegador Tor e o Tails fornecem ferramentas como o HTTPS Everywhere, para garantir uma conexão criptografada entre o nó de saída e o servidor de destino sempre que for possível.
Fingir ser o servidor de destino, com uma técnica conhecida como ataque machine-in-the-middle (MitM). É por isso que você deve prestar ainda mais atenção aos avisos de segurança no Navegador Tor. Se você receber algum desses avisos, use a ferramenta de Nova Identidade do Navegador Tor para mudar de nó de saída.
Para saber mais sobre quais informações ficam disponíveis para quem possa observar diferentes partes de um circuito Tor, veja o gráfico interativo em Tor FAQ: Nós de saída podem escutar as comunicações?.
Nós de saída do Tor já foram usados no passado para coletar dados sensíveis de conexões não criptografadas. Nós de saída maliciosos geralmente são identificados e removidos da rede Tor. Por exemplo, veja Ars Technica: Um profissional de segurança usou Tor para coletar senhas de emails governamentais.
Adversários que conseguem monitorar ambas as pontas de um circuito Tor podem conseguir identificar usuários
Um adversário que conseguisse controlar os 3 retransmissores de um circuito poderia desanonimizar usuários Tor.
Tor escolhe para cada circuito 3 retransmissores pertencentes a 3 operadores de rede diferentes.
Tails ainda toma outras medidas para usar circuitos diferentes para aplicações diferentes.
A rede Tor possui mais de 6.000 retransmissores. Organizações que rodam retransmissores Tor incluem universidades como o MIT, grupos de ativistas como Riseup, organizações sem fins lucrativos como Derechos Digitales, empresas de hospedagem de internet como Private Internet Access, e assim por diante. A imensa diversidade de pessoas e organizações que rodam retransmissores Tor tornam a rede mais segura e mais sustentável.
Um adversário poderoso, que possa cronometrar e analisar o perfil do tráfego que entra e sai da rede Tor, pode conseguir desanonimizar usuários da rede Tor. Esses ataques são chamados ataques de correlação de ponta-a-ponta, pois o atacante precisa observar ambas as pontas do circuito Tor ao mesmo tempo.
Nenhuma rede de anonimato utilizada para conexões rápidas, tipo para navegação na Internet ou para conversas por mensagens instantâneas, tem como proteger 100% de ataques de correlação ponta-a-ponta. Nesse caso, VPNs (redes virtuais privadas) são menos seguras que Tor, pois não utilizam três retransmissores independentes.
Ataques de correlação ponta-a-ponta foram estudados em artigos de pesquisa, mas nós não temos conhecimento de que tenham sido de fato usados para desanonimizar usuários da rede Tor. Para um exemplo, veja Murdoch e Zieliński: Sampled Traffic Analysis by Internet-Exchange-Level Adversaries (em inglês).
Reduzindo riscos ao usar computadores não confiáveis
Instale Tails a partir de um computador no qual você confie
Tails te protege de vírus e malware que estejam presentes no seu sistema operacional usual. Isso ocorre porque o Tais roda independentemente de outros sistemas operacionais.
Mas seu Tails pode ser corrompido caso você o instale a partir de um sistema operacional comprometido. Para reduzir esse risco:
Sempre instale Tails a partir de um sistema operacional confiável. Por exemplo, baixe o Tails em um computador sem vírus, ou clone o Tails de um amigo confiável.
Não conecte o seu pendrive USB com Tails enquanto outro sistema operacional estiver sendo executado no computador.
Use o seu pendrive USB com Tails apenas para executar o Tails. Não use o mesmo pendrive para transferir arquivos de ou para outro sistema operacional.
Se você se preocupa com a possibilidade de que seu Tails esteja corrompido, faça uma atualização manual a partir de um sistema operacional confiável.
Não temos conhecimento de nenhum vírus capaz de infectar uma instalação de Tails, mas é possível que um seja criado no futuro.
Nenhum sistema operacional pode proteger contra modificações no hardware
O computador pode estar comprometido caso seus componentes físicos tenham sido alterados. Por exemplo, se um grampo de teclado tiver sido fisicamente instalado no computador, suas senhas, informações pessoais e outros dados digitados no teclado, podem ser armazenados e acessados por outras pessoas, mesmo que você esteja usando Tails.
Tente manter seu computador em um local seguro. Alterações no hardware são mais prováveis em computadores públicos, cafés ou bibliotecas com Internet e em computadores desktop (de gabinete), nos quais é mais fácil esconder um dispositivo.
Se a possibilidade de que seu computador tenha sido modificado te preocupa:
Use um gerenciador de senhas para copiar e colar as senhas salvas. Desse modo, você não precisa digitar as senhas e assim pode evitar que elas sejam vistas por pessoas ou câmeras perto de você.
Use o Teclado Virtual, se você estiver usando um computador público ou tenha a preocupação que o computador possa ter um keylogger.
Keyloggers são fáceis de comprar e esconder em computadores de gabinete, mas não em laptops. Por exemplo, veja KeeLog: KeyGrabber forensic keylogger getting started (em inglês).
Outras alterações de hardware são muito mais complicadas e caras de instalar. Por exemplo, veja Ars Technica: Fotos de uma fábrica de "atualização" da NSA mostram roteador da Cisco recebendo um implante (em inglês).
Nenhum sistema operacional pode se proteger de ataques na BIOS e no firmware
Firmware inclui a BIOS ou UEFI e outros programas armazenados em chips eletrônicos do computador. Todos os sistemas operacionais, incluindo Tails, dependem do firmware para iniciarem e rodarem, então nenhum sistema operacional pode se proteger de um ataque ao firmware. Da mesma maneira que um carro depende da qualidade da rua em que ele está andando, sistemas operacionais dependem de seus firmwares.
Manter seu computador em um local seguro pode te proteger de algum ataque de firmware, mas alguns outros ataques de firmware podem ser executados remotamente.
ataques de firmware já foram demonstrados, mas são complicados e caros de se realizarem. Nós não conhecemos nenhum uso contra usuários Tails. Por exemplo, veja LegbaCore: Roubando chaves/emails GPG no Tails através de infecção remota de firmware (em inglês).
Pelo fato de que você sempre tem que adaptar suas práticas de segurança digital para necessidades e ameaças específicas, recomendamos que você aprenda mais fazendo a leitura dos seguintes guias:
