- doc
- anonymous internet
- Navegar por la web con el Navegador Tor
- Proxy server refusing connections
- Confinamiento de AppArmor, descargar y subir archivos
- Hiding that you are using Tor Browser
- Cifrado HTTPS con HTTPS Everywhere
- Protección contra los peligros de JavaScript
- Nivel de seguridad
- Circuito Tor
- Funcionalidad de Nueva identidad
- NoScript para tener aún más control sobre el JavaScript
- Letterboxing
El Navegador Tor es un navegador web basado en Mozilla Firefox, configurado para proteger tu privacidad.
![]()
Enviar tus conexiones a sitios web a través de la red Tor no es suficiente para protegerte totalmente mientras navegas la web:
Se pueden usar cookies para seguirte e identificarte a través de distintos sitios web.
Se han utilizado vulnerabilidades de seguridad en Javascript para desanonimizar el Navegador Tor anteriormente.
Es por eso que el Navegador Tor integra todo tipo de protecciones de seguridad dentro del navegador.
Puedes encontrar algunas preguntas frecuentes sobre el Navegador Toren el FAQ.
Proxy server refusing connections
The following error message in Tor Browser means that Tails is not yet connected to the Tor network:
The proxy server is refusing connections
Make sure that you are:
Confinamiento de AppArmor, descargar y subir archivos
Tor Browser can only read and write to the following folders:
- Documents - Downloads - Music - Pictures - Videos - Tor Browser - Persistent/Tor Browser, if you have a Persistent Storage
This is because, in Tails, Tor Browser is confined using AppArmor to protect your files from some types of attacks against Tor Browser.
For example, thanks to this confinement, even if an attacker manages to exploit a security vulnerability in Tor Browser, they wouldn't be able to access all the content of your Persistent Storage.
This is why you get the following error if you try to download files to another folder:
Could not read the contents of folder.
Error opening directory folder: Permission denied
If you want to download a file from Tor Browser, save it to one of these folders.
If you want to upload a file from Tor Browser, copy it first to one of these folders.
Para evitar que Tails se quede sin memoria y se bloquee, descarga los archivos grandes en la carpeta Persistent/Tor Browser. Todos los archivos que descargues fuera del Almacenamiento Persistente se descargan en la memoria (RAM), que está más limitada.
Hiding that you are using Tor Browser
It is impossible to hide to the websites that you visit that you are using Tor, because the list of exit nodes of the Tor network is public.
That is why many more websites ask you to solve a CAPTCHA when using Tor Browser.
The anonymity provided by Tor Browser works by making all users look the same to make it impossible to know who is who among the millions of users of Tor Browser.
Tails tries to make it as difficult as possible for websites to distinguish Tails users from other users of Tor Browser. If it was possible for a website to determine whether you are a user of Tor Browser inside or outside of Tails, this would provide a little bit more information about you and reduce your anonymity.
The websites that you visit can retrieve a lot of information about your browser, whether it's Tor Browser or a regular browser. This information is called the fingerprint of the browser and includes the name and version of the browser, the size of the window, the time zone, the available fonts, etc.
To make it difficult to distinguish Tails users from other users of Tor Browser, Tor Browser in Tails tries to provide the same information as Tor Browser on other operating systems.
A difference is that Tails includes the uBlock Origin extension, which removes advertisements. If an attacker can determine that you are not downloading the advertisements that are included in a webpage, that could reveal that you are a Tails user.
To hide to someone monitoring your Internet connection that you are connecting to Tor, see our documentation about connecting to the Tor network.
Cifrado HTTPS con HTTPS Everywhere
Using HTTPS instead of HTTP encrypts your communications with the website and prevents the Tor exit node from intercepting your communications.
Por ejemplo, así aparece el navegador cuando intentamos entrar en una cuenta de correo electrónico de riseup.net, usando su servicio de web:
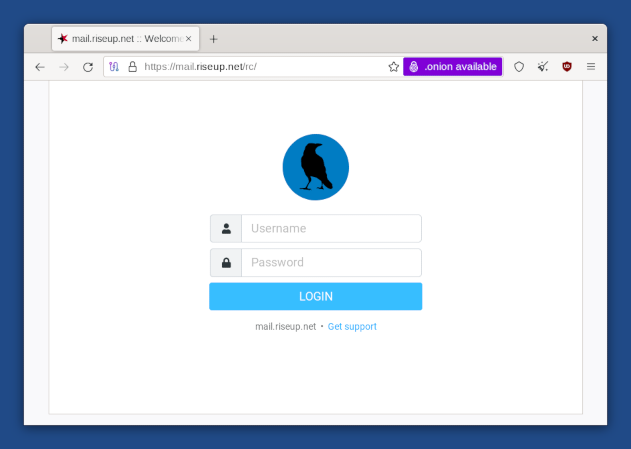
Fíjate en el icono del candado a la izquierda de la barra de direcciones que dice "mail.riseup.net" y la dirección que comienza por "https://" (en lugar de "http://"). Esto indica que se está usando una conexión cifrada con HTTPS.
Cuando envíes u obtengas información confidencial (como contraseñas) deberías intentar sólo usar servicios que provean HTTPS. De lo contrario, es muy fácil para un espía robar cualquier información que estés enviando o modificar el contenido de una página de camino a tu navegador.
HTTPS Everywhere es una extensión de Firefox incluida en el Navegador Tor. Es realizada como una colaboración entre The Tor Project y la Electronic Frontier Fundation. Cifra tus comunicaciones con un gran número de sitios web. Muchos sitios en la web ofrecen un soporte limitado para el cifrado sobre HTTPS, pero lo hacen difícil de usar. Por ejemplo, pueden pasar a HTTP no cifrado, o poner enlaces que regresan al sitio no cifrado en sus páginas cifradas. La extensión HTTPS Everywhere corrige estos problemas al reescribir todas las solicitudes a estos sitios sobre HTTPS.
Para aprender más sobre HTTPS Everywhere puedes leer:
Protección contra los peligros de JavaScript
Teniendo todo el JavaScript desactivado por defecto desactivaría mucho JavaScript inofensivo y posiblemente útil, y podría inutilizar muchos sitios web.
Por eso es que el JavaScript está habilitado por defecto pero el Navegador Tor deshabilita todo el JavaScript potencialmente peligroso. Consideramos que este es un compromiso necesario entre la seguridad y la usabilidad.
Para entender mejor el comportamiento del Navegador Tor, por ejemplo en lo que respecta al JavaScript y a las cookies, puedes consultar el documento de diseño del Navegador Tor.
Nivel de seguridad
Puedes cambiar el nivel de seguridad del Navegador Tor para desactivar las funcionalidades del navegador como equilibrio entre seguridad y usabilidad. Por ejemplo, puedes fijar el nivel de seguridad en El más seguro de todos para desactivar el JavaScript por completo.
El nivel de seguridad está fijado en Estándar por defecto, que da la mejor experiencia de uso.
To change the security level, click on the ![]() icon on the right of the address bar
and choose Settings….
icon on the right of the address bar
and choose Settings….
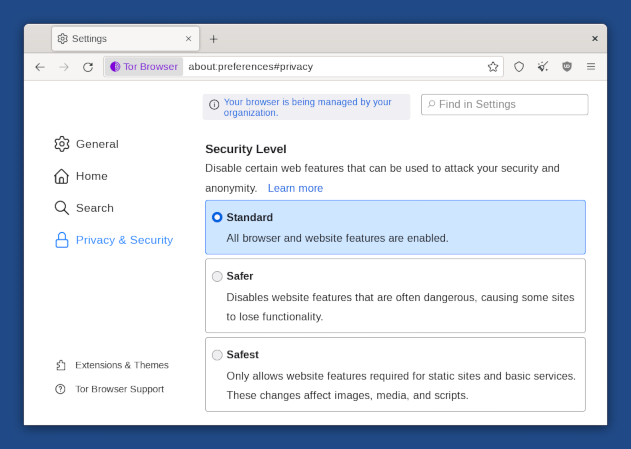
You can safely disregard the message, "Your browser is being managed by your organization," which appears in the Tor Browser preferences.
All this message means is that the automatic updates feature of Tor Browser has been disabled. This is done intentionally in Tails to make sure that no security feature or configuration gets broken by automatic updates of Tor Browser.
Circuito Tor
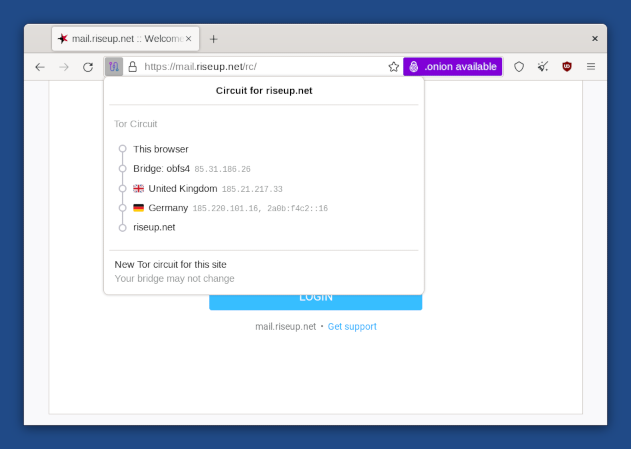
Haz click en el candado en la barra de direcciones para ver el circuito Tor que está siendo utilizado para conectarse al sitio web en la pestaña actual, son 3 repetidores, sus respectivos países y direcciones IP.
El último repetidor del circuito, que está justo antes del sitio web de destino, es el repetidor de salida. El país en el que está puede influir en cómo se comporta el sitio web.
Haz click en el botón Nuevo Circuito Tor para este Sitio para usar un circuito distinto.
You can use Onion Circuits to get more detailed information about the circuits being used.
Funcionalidad de Nueva identidad
To switch to a new identity, choose ![]() ▸ New identity.
▸ New identity.
The New Identity feature of Tor Browser:
Closes all open tabs.
Clears the session state including cache, history, and cookies.
Closes all existing web connections and creates new Tor circuits.
This feature is not enough to strongly separate contextual identities as the Tor circuits used ouside of Tor Browser are not changed.
Restart Tails instead.
Para mas detalles, consulta el diseño e implementación del Navegador Tor.
NoScript para tener aún más control sobre el JavaScript
Tor Browser includes the NoScript extension to:
Protege de más ataques de JavaScript. Por ejemplo, ataques de cross-site scripting (XSS).
Allow you to disable JavaScript completely on some websites only.
Para más información puedes revisar el sitio web de NoScript y sus funcionalidades.
Letterboxing
The letterboxing feature of Tor Browser helps to prevent websites from identifying your browser based on the size of its window. Without letterboxing, websites could use the size of the browser window to track visitors or weaken your anonymity.
The letterboxing feature of Tor Browser works by adding gray margins to the browser window when the window is resized. The webpage remains as close as possible to the desired size without revealing the actual size of the window.
